Nextcloud 20 run in docker with php-fpm,nginx-backend and nginx proxy
Create docker-compose.yml swarm
---
version: '3.5'
services:
nginx-backend:
image: registry.gitlab.com/devops_containers/dockers/nginx:1.19.6-alpine-libressl
hostname: nginx
volumes:
- "./configs/nginx:/etc/nginx"
- "./data:/data"
ports:
- target: 80
published: 82
protocol: tcp
mode: host
environment:
- "TZ=Asia/Yekaterinburg"
networks:
pxc_8_pxc8-net:
mysql_8_mysql8-net:
app_app-network:
aliases:
- nginx-backend-itc-life
deploy:
replicas: 1
restart_policy:
condition: any
delay: 5s
max_attempts: 130
window: 12s
update_config:
parallelism: 1
delay: 10s
failure_action: continue
monitor: 10s
max_failure_ratio: 0.3
placement:
constraints: [ node.role == manager ]
php-fpm:
image: registry.gitlab.com/devops_containers/dockers/php:7.4.15-fpm-alpine3.12
hostname: php-fpm
volumes:
- "./data:/data"
- "./configs/php-fpm/php-fpm.d/:/usr/local/etc/php-fpm.d"
- "./configs/php-fpm/php:/usr/local/etc/php"
environment:
TZ: "Asia/Yekaterinburg"
networks:
pxc_8_pxc8-net:
mysql_8_mysql8-net:
redis_redis-network:
app_app-network:
aliases:
- php-fpm-itc-life
deploy:
replicas: 1
restart_policy:
condition: any
delay: 5s
max_attempts: 130
window: 12s
update_config:
parallelism: 1
delay: 10s
failure_action: continue
monitor: 10s
max_failure_ratio: 0.3
placement:
constraints: [ node.role == manager ]
networks:
pxc_8_pxc8-net:
driver: overlay
external: true
mysql_8_mysql8-net:
driver: overlay
external: true
app_app-network:
driver: overlay
external: true
redis_redis-network:
driver: overlay
external: true
Nginx backend config
set_real_ip_from 10.0.0.0/8;
set_real_ip_from 172.16.0.0/12;
set_real_ip_from 192.168.0.0/16;
real_ip_header X-Real-IP;
upstream php-handler {
server php-fpm:9002;
}
server {
listen 80;
server_name
nc.itc-life.ru
;
root /data/hosting/nc/public_html;
# set max upload size
client_max_body_size 10G;
fastcgi_buffers 64 4K;
# Enable gzip but do not remove ETag headers
gzip on;
gzip_vary on;
gzip_comp_level 4;
gzip_min_length 256;
gzip_proxied expired no-cache no-store private no_last_modified no_etag auth;
gzip_types application/atom+xml application/javascript application/json application/ld+json application/manifest+json application/rss+xml application/vnd.geo+json application/vnd.ms-fontobject application/x-font-ttf application/x-web-app-manifest+json application/xhtml+xml application/xml font/opentype image/bmp image/svg+xml image/x-icon text/cache-manifest text/css text/plain text/vcard text/vnd.rim.location.xloc text/vtt text/x-component text/x-cross-domain-policy;
# Pagespeed is not supported by Nextcloud, so if your server is built
# with the `ngx_pagespeed` module, uncomment this line to disable it.
#pagespeed off;
# HTTP response headers borrowed from Nextcloud `.htaccess`
add_header Referrer-Policy "no-referrer" always;
add_header X-Content-Type-Options "nosniff" always;
add_header X-Download-Options "noopen" always;
add_header X-Frame-Options "SAMEORIGIN" always;
add_header X-Permitted-Cross-Domain-Policies "none" always;
add_header X-Robots-Tag "none" always;
add_header X-XSS-Protection "1; mode=block" always;
# Remove X-Powered-By, which is an information leak
fastcgi_hide_header X-Powered-By;
# Path to the root of your installation
# Specify how to handle directories -- specifying `/index.php$request_uri`
# here as the fallback means that Nginx always exhibits the desired behaviour
# when a client requests a path that corresponds to a directory that exists
# on the server. In particular, if that directory contains an index.php file,
# that file is correctly served; if it doesn't, then the request is passed to
# the front-end controller. This consistent behaviour means that we don't need
# to specify custom rules for certain paths (e.g. images and other assets,
# `/updater`, `/ocm-provider`, `/ocs-provider`), and thus
# `try_files $uri $uri/ /index.php$request_uri`
# always provides the desired behaviour.
index index.php index.html /index.php$request_uri;
# Default Cache-Control policy
expires 1m;
# Rule borrowed from `.htaccess` to handle Microsoft DAV clients
location = / {
if ( $http_user_agent ~ ^DavClnt ) {
return 302 /remote.php/webdav/$is_args$args;
}
}
location = /robots.txt {
allow all;
log_not_found off;
access_log off;
}
location ^~ /apps/rainloop/app/data {
deny all;
}
# Make a regex exception for `/.well-known` so that clients can still
# access it despite the existence of the regex rule
# `location ~ /(\.|autotest|...)` which would otherwise handle requests
# for `/.well-known`.
location ^~ /.well-known {
# The following 6 rules are borrowed from `.htaccess`
rewrite ^/\.well-known/host-meta\.json /public.php?service=host-meta-json last;
rewrite ^/\.well-known/host-meta /public.php?service=host-meta last;
rewrite ^/\.well-known/webfinger /public.php?service=webfinger last;
rewrite ^/\.well-known/nodeinfo /public.php?service=nodeinfo last;
location = /.well-known/carddav { return 301 /remote.php/dav/; }
location = /.well-known/caldav { return 301 /remote.php/dav/; }
try_files $uri $uri/ =404;
}
# Rules borrowed from `.htaccess` to hide certain paths from clients
location ~ ^/(?:build|tests|config|lib|3rdparty|templates|data)(?:$|/) { return 404; }
location ~ ^/(?:\.|autotest|occ|issue|indie|db_|console) { return 404; }
# Ensure this block, which passes PHP files to the PHP process, is above the blocks
# which handle static assets (as seen below). If this block is not declared first,
# then Nginx will encounter an infinite rewriting loop when it prepends `/index.php`
# to the URI, resulting in a HTTP 500 error response.
location ~ \.php(?:$|/) {
rewrite ^/(?!index|remote|public|cron|core\/ajax\/update|status|ocs\/v[12]|updater\/.+|oc[ms]-provider\/.+|.+\/richdocumentscode\/proxy) /index.php$request_uri;
fastcgi_split_path_info ^(.+?\.php)(/.*)$;
set $path_info $fastcgi_path_info;
try_files $fastcgi_script_name =404;
include fastcgi_params;
fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name;
fastcgi_param PATH_INFO $path_info;
fastcgi_param HTTPS on;
fastcgi_param modHeadersAvailable true; # Avoid sending the security headers twice
fastcgi_param front_controller_active true; # Enable pretty urls
fastcgi_pass php-handler;
fastcgi_intercept_errors on;
fastcgi_request_buffering off;
fastcgi_read_timeout 180;
fastcgi_send_timeout 180;
}
location ~ \.(?:css|js|svg|gif)$ {
try_files $uri /index.php$request_uri;
expires 6M; # Cache-Control policy borrowed from `.htaccess`
access_log off; # Optional: Don't log access to assets
}
location ~ \.woff2?$ {
try_files $uri /index.php$request_uri;
expires 7d; # Cache-Control policy borrowed from `.htaccess`
access_log off; # Optional: Don't log access to assets
}
location / {
try_files $uri $uri/ /index.php$request_uri;
}
}
Nginx proxy config with ssl
server {
listen 80;
server_name
nc.itc-life.ru
;
return 301 https://nc.itc-life.ru$request_uri;
}
server {
listen 443 ssl http2;
server_name
nc.itc-life.ru
;
include /etc/nginx/ssl.d/itc-life.ru/ssl.itc-life.ru.conf;
location ^~ /.well-known/acme-challenge/ {
root /var/www/letsencrypt;
}
location /.well-known/carddav {
return 301 $scheme://$host/remote.php/dav;
}
location /.well-known/caldav {
return 301 $scheme://$host/remote.php/dav;
}
location / {
add_header Strict-Transport-Security "max-age=15768000; includeSubDomains; preload;";
proxy_headers_hash_max_size 512;
proxy_headers_hash_bucket_size 64;
proxy_set_header Host $host;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_connect_timeout 1200;
proxy_send_timeout 12000;
proxy_read_timeout 18000;
add_header Front-End-Https on;
# whatever the IP of your cloud server is
proxy_pass http://nginx-backend:80;
client_max_body_size 10G;
}
}
Php-fpm config
[global]
error_log = /proc/self/fd/2
[www]
user = www-data
group = www-data
listen.owner = www-data
listen.group = www-data
listen = 9001
pm = dynamic
pm.max_children = 50
pm.start_servers = 5
pm.min_spare_servers = 5
pm.max_spare_servers = 40
request_terminate_timeout = 300
pm.max_requests = 300
;rlimit_files = 131072
rlimit_core = unlimited
clear_env = no
php_admin_flag[short_open_tag] = on
php_admin_value[date.timezone] = Asia/Yekaterinburg
php_value[memory_limit] = 2560M
php_admin_value[memory_limit] = 2560M
php_value[max_file_uploads] = 550
php_value[upload_max_filesize] = 200M
php_value[post_max_size] = 200M
pm.status_path = /status
catch_workers_output = yes
php_flag[display_errors] = on
php_admin_value[error_reporting] = E_ALL & ~E_NOTICE & ~E_WARNING & ~E_STRICT & ~E_DEPRECATED
access.log = /proc/self/fd/2
php_admin_flag[log_errors] = on
request_slowlog_timeout = 1
slowlog = /proc/self/fd/2Install owncloud in docker container php-fpm after start
Download
mkdir -p /data/hosting/nc/
cd /data/hosting/nc/
curl -L https://download.nextcloud.com/server/releases/latest.tar.bz2 -o /data/hosting/nc/latest.tar.bz2
tar -xvf latest.tar.bz2
mv nextcloud public_html
chown -R www-data:www-data /data/hosting/nc/And complete install in web
Snippets
Integrate nextcloud with openldap
Enable openldap
su -s /bin/bash -c 'cd /data/hosting/nc/public_html/ && ./occ app:enable user_ldap' www-dataEdit file
apps/user_ldap/ajax/getConfiguration.php<?php
/**
* @copyright Copyright (c) 2016, ownCloud, Inc.
*
* @author Arthur Schiwon <blizzz@arthur-schiwon.de>
* @author Christoph Wurst <christoph@winzerhof-wurst.at>
* @author Joas Schilling <coding@schilljs.com>
* @author Juan Pablo Villafáñez <jvillafanez@solidgear.es>
* @author Lukas Reschke <lukas@statuscode.ch>
* @author Morris Jobke <hey@morrisjobke.de>
* @author Roeland Jago Douma <roeland@famdouma.nl>
*
* @license AGPL-3.0
*
* This code is free software: you can redistribute it and/or modify
* it under the terms of the GNU Affero General Public License, version 3,
* as published by the Free Software Foundation.
*
* This program is distributed in the hope that it will be useful,
* but WITHOUT ANY WARRANTY; without even the implied warranty of
* MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
* GNU Affero General Public License for more details.
*
* You should have received a copy of the GNU Affero General Public License, version 3,
* along with this program. If not, see <http://www.gnu.org/licenses/>
*
*/
// Check user and app status
require_once($_SERVER['DOCUMENT_ROOT'].'/lib/base.php');
\OC_JSON::checkAdminUser();
\OC_JSON::checkAppEnabled('user_ldap');
\OC_JSON::callCheck();
$prefix = (string)$_POST['ldap_serverconfig_chooser'];
$ldapWrapper = new OCA\User_LDAP\LDAP();
$connection = new \OCA\User_LDAP\Connection($ldapWrapper, $prefix);
$configuration = $connection->getConfiguration();
if (isset($configuration['ldap_agent_password']) && $configuration['ldap_agent_password'] !== '') {
// hide password
$configuration['ldap_agent_password'] = '**PASSWORD SET**';
}
\OC_JSON::success(['configuration' => $configuration]);
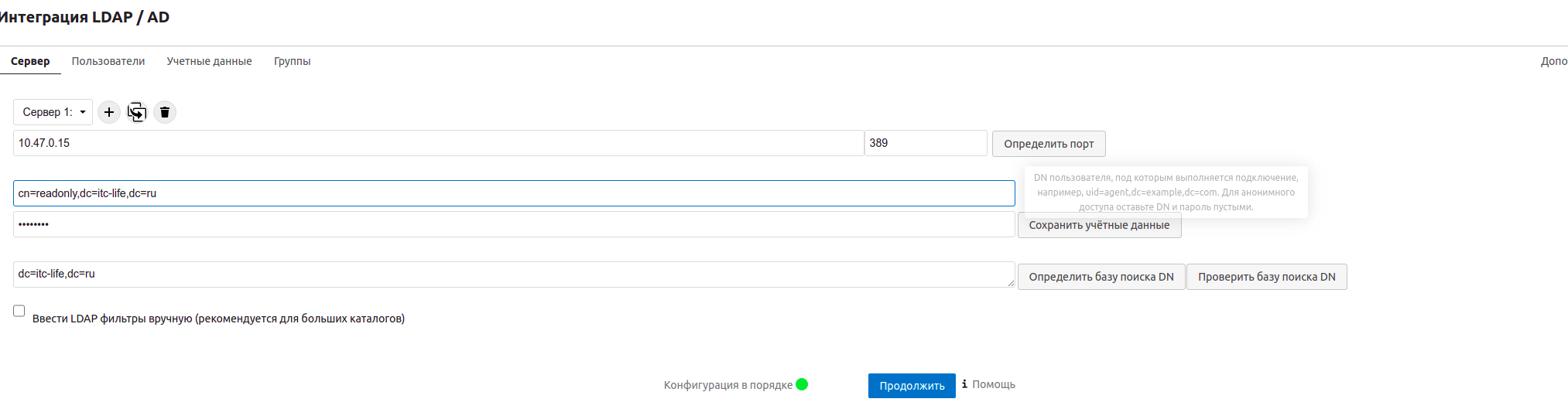
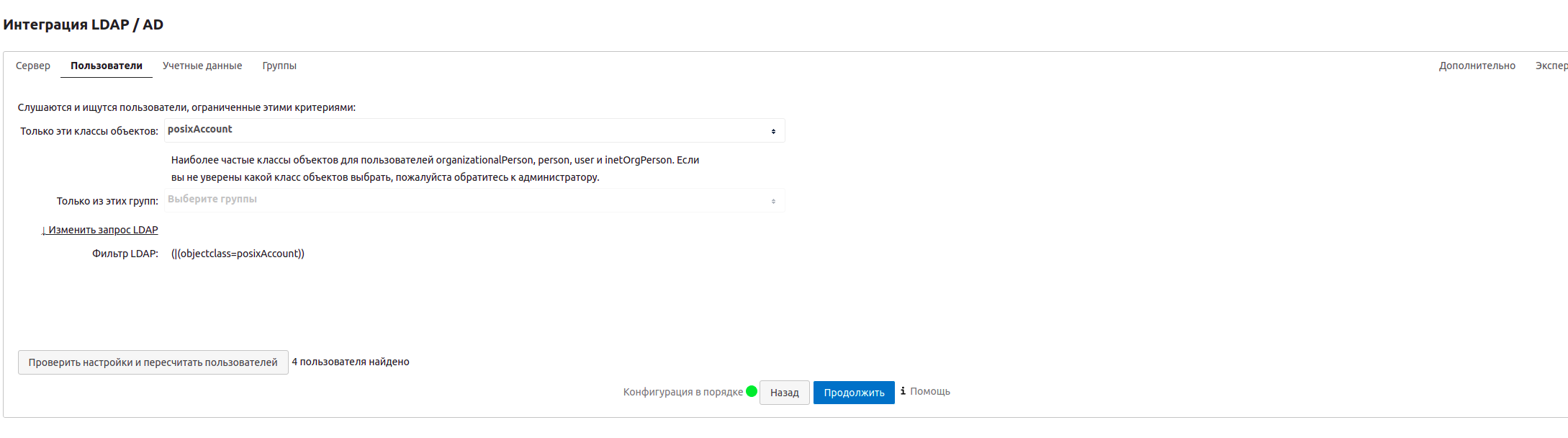
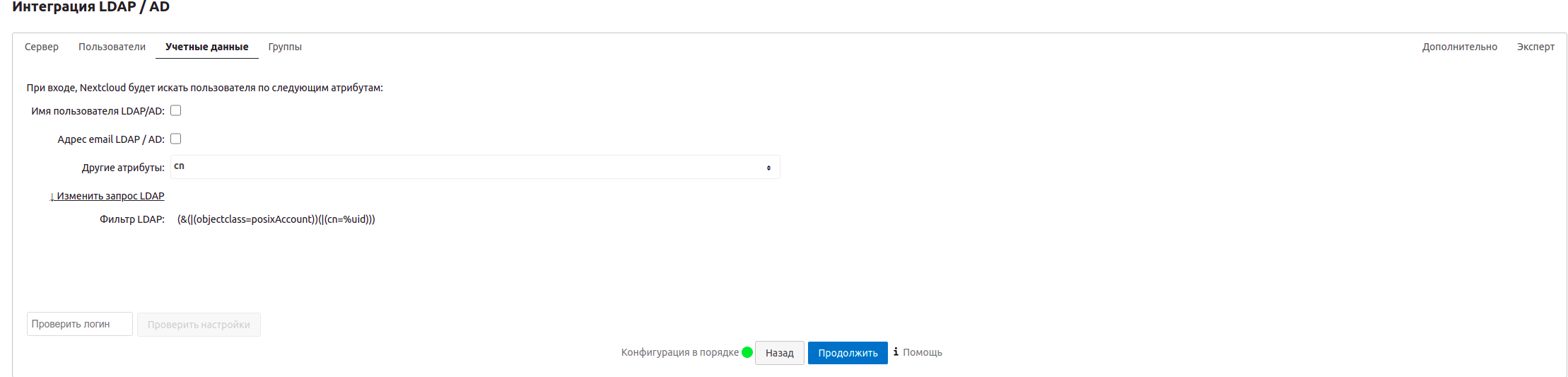
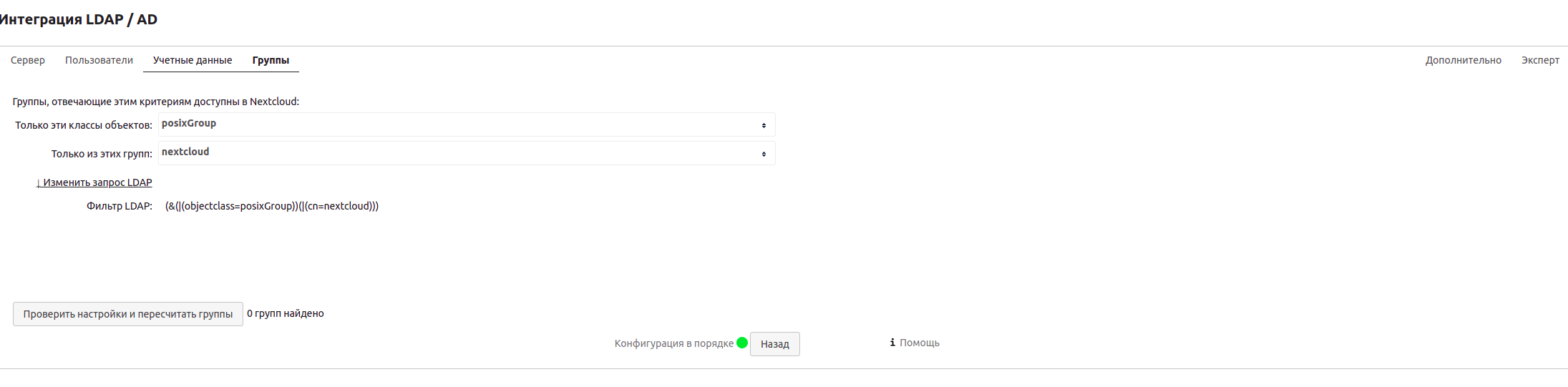
Configure openldap in admin page
https://nc.itc-life.ru/settings/admin/ldap